The road to SOC 2 Type 2 compliance
In August 2022, Checkly's security team successfully implemented and documented all necessary security controls to be SOC 2 compliant for the first time. To get our SOC 2 Type 1 report we had to prove that our engineering, HR, operational, and IT security processes met the high level of information security SOC 2 compliance demands to an accredited auditing firm.
While this has been a noteworthy effort, moving forward we also had to ensure our security controls operated effectively from August until now.
The SOC 2 Type 2 audit ensures that Checkly is committed to an ongoing compliance effort and can maintain those high security standards indefinitely. Independent auditors thoroughly check that we solve security tickets according to our internal SLAs, while the security team regularly meets and plans future compliance efforts.
What does SOC 2 Type 2 compliance mean for our customers?
As was the case with the completion of our SOC 2 Type 1 audit, our customers and users can be assured there has been an independent and full review of Checkly’s security and privacy practices.
The Checkly synthetic monitoring platform evolves at a breathtaking pace, which you can see from our frequent change notes, launch week events, regular social media updates and, of course, when you use Checkly. With the successful completion of our SOC 2 Type 2 audit, we’ve proven as a company that we can move quickly and simultaneously implement a high degree of information security.
To be more specific, we’ve done the following:
- Successfully passed a review by an AICPA-accredited third-party auditing firm that reviewed evidence for over 120 compliance controls and found no deviations.
- Completed a manual Pentest by a certified third-party pentester, with the only medium severity finding fixed within 2 days of discovery.
- Employed DevSecOps tools that continuously review security settings.
- Fixed security issues within our auditor-approved SLA for resolution.
What's next?
Our SOC 2 Type 2 audit might be completed, but work for the cross-functional Checkly information security team is never over. We’re already planning and coordinating this year's compliance tasks and security enhancements to prepare for our next compliance audit.
As part of that ongoing security effort, we will:
- Continue to run incident response and disaster recovery exercises.
- Regularly assess information security risks.
- Review the security standards of all of our third party vendors.
- Plan and implement technical platform security improvements.
The Checkly SOC 2 Type 2 report is now available upon request by emailing sales@checklyhq.com. Have questions? Contact us!
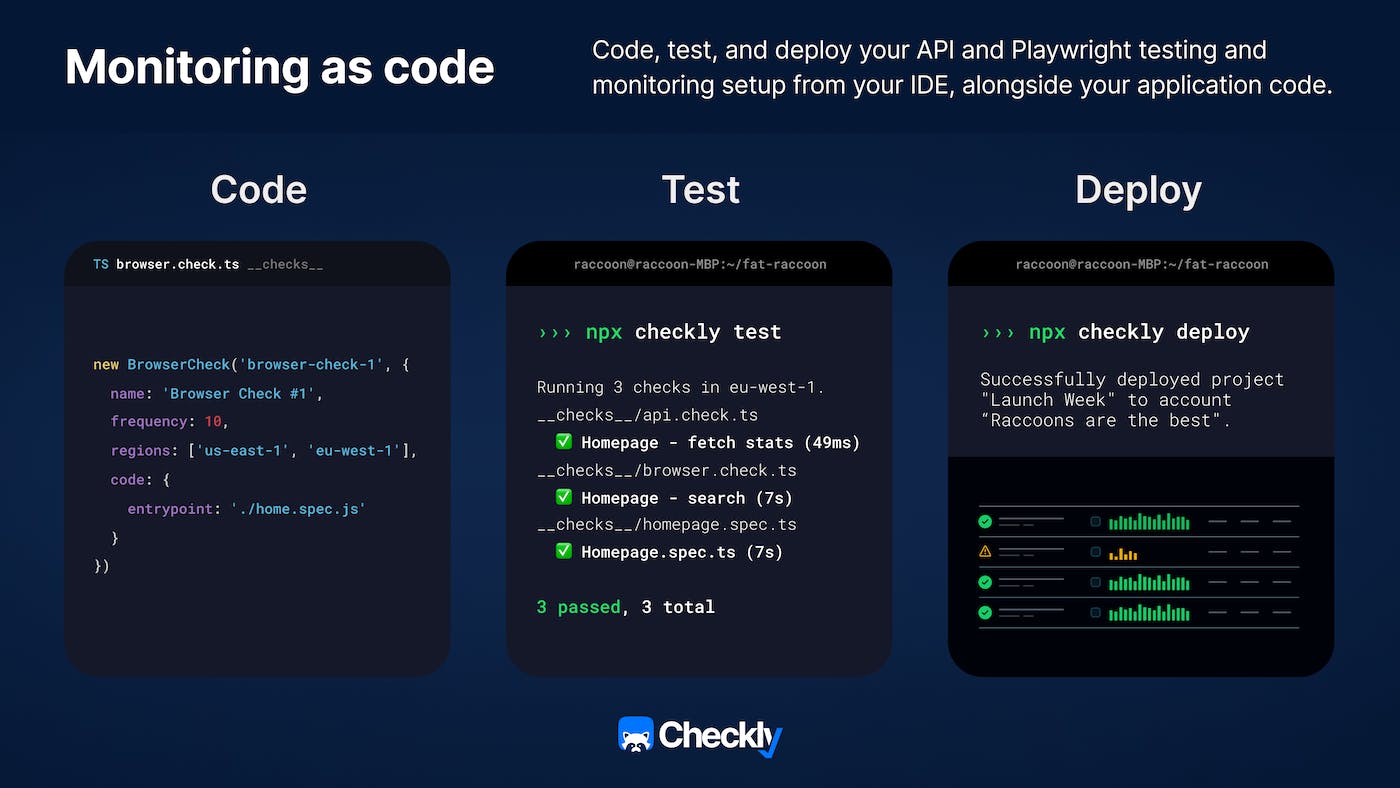
And that’s a wrap on all the exciting things that we announced for Launch Week 2. If you’d like a recap of all of the news we announced this week, check out our overview blog post and our Launch Week 2 playlist on YouTube. Finally, don’t forget to enter your monitoring as code project for a chance to win our $500 home makeover giveaway.